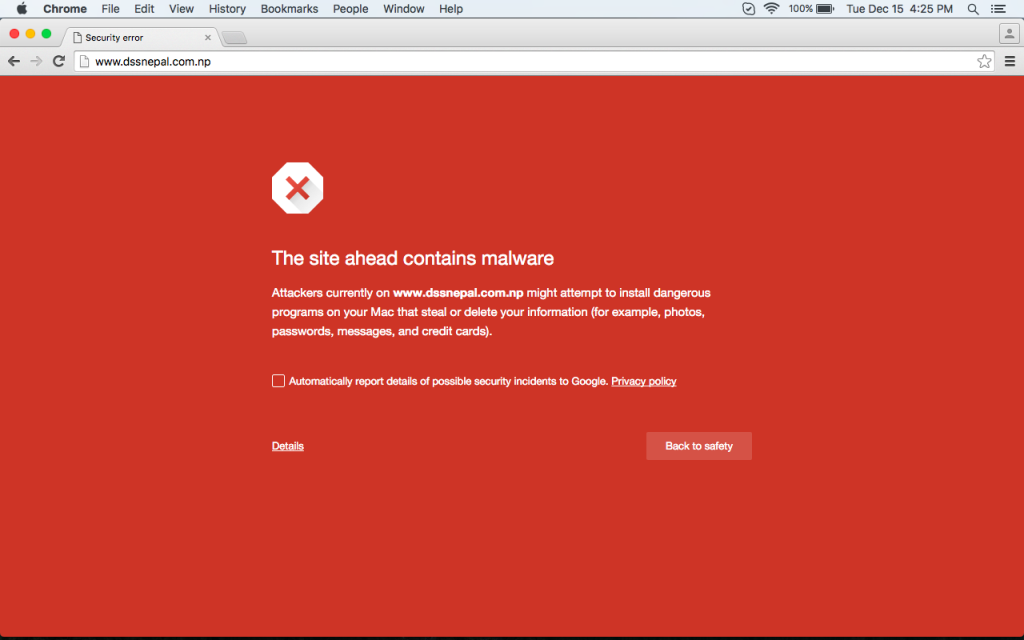
Google is policing the content presented in its search engine results. The “Reported Attack Site!” warning page you see on your site is because Google has detected malicious content on your site. In short, your site has been hacked.
To find out the details of what Google found, click on the button titled “Why was this site blocked?“. A new page will display a breakdown of questionable content, including a list of affected web pages and the infections on those pages.
To learn more, please visit:
Fixing the Problem
Change your Password
The first thing you need to do is change your cPanel/FTP password. Since the Google warning might also block access to your cPanel, you should try accessing the site via the server’s hostname.
To open a support ticket, please log in to your Trafficpullz Please login to your Galaxy Dashboard:: https://galaxy.trafficpullz.com
Send the ticket to the Support department, and include the primary domain name on your account as well as the request to reset your cPanel password. Please indicate you are doing this because your site was hacked and you need a *new* password, not the original cPanel password reinstated.
Remove Affected Files
You will need to remove the affected web pages (and other files) by:
- Deleting or cleaning the pages/files
- Uploading uninfected copies of the pages/files to your site via FTP. Despite the Google block, you should still have FTP access to your site.
- If you need assistance with the cleanup we would recommend you look at our SiteLock Service:
https://www.trafficpullz.com/site-lock-security/
NOTE: If you are using Soholaunch, WordPress, Joomla or a Content Management System that requires you to log into an Admin section of your website, you may not be able to restore your site until after Google removes the warning (you will not otherwise be able to use the proper tools).
If you want to be absolutely sure all the malicious content is gone, you can request an “account reset”. This will erase *everything* on your account: web pages, emails, databases, settings, etc. You may then upload a new copy of your site and recreate your email addresses. Please make sure that you have a backup for your site before requesting this.
To request an account reset, please submit a ticket.
To open a support ticket, please log in to your Trafficpullz Galaxy Dashboard: https://galaxy.trafficpullz.com
The ticket should go to the Support department, and should specifically state that you want an account reset. Following that, you will receive an email asking you to confirm that you want your account reset and you will need to reply to this email to confirm some information. Once confirmed, our Tech Support department can proceed with your request.
Request a Review
From Google:
You can request that Google take another look at your site. You will need to do this from a Google Webmaster Tools account. If you do not have one, you can create a new one for free here:
https://www.google.com/webmasters/tools/
You will need to upload a web page with a special code that will allow Google to verify that you are the legitimate owner of the account. Once that’s been done, you can request a review from inside your Webmaster Account by following these steps:
On the Webmaster Tools Home page, select the site you want.
Click “Diagnostics” and then click “Malware.”
Click “Request a review.”
The review will be done within the next 24 hours. If nothing malicious is found on your site, Google will remove the warning. If more malicious content is found, the warning will remain in place and the report page will be updated to reflect the new discoveries.
From StopBadware:
The advantage to using StopBadware is that you do not have to create a Google Webmaster account in order to have the warning removed. To request an independent review by StopBadware (instructions copied from stopbadware.org):
- Search for your site in the Badware Website Clearinghouse: https://www.stopbadware.org/clearinghouse/search
- Find your site in the search results and click the link for your site. You will be taken to the StopBadware.org report page for your site.
- Click the “Request an independent review of partners’ findings” button underneath the “Current Activity” section of the report.
- Fill out and submit the review form.
Please note: As part of the review process, information submitted in the StopBadware.org review form will be shared with Google.
Change All Remaining Passwords
Once the warning is removed, please log in to your cPanel and change any other passwords you have. For scripts like Soholaunch, WordPress, Joomla, etc., you will need to log in to the website’s Admin area to change the passwords.
- Log in to your Trafficpullz dashboard: https://galaxy.trafficpullz.com
- Click on “My cPanel”. If you have more than one domain associated with your HostPapa account, click on the appropriate domain link, then enter your cPanel password if required.
Ignoring The Google Warning:
We strongly suggest you do not select this option.
There is a tiny text link on the Google Warning page that states: “Ignore this warning”. If you click on it, you may be able to access your site but you will expose your computer to whatever has infected your site. If it is a new form of malicious software, there is no guarantee that your anti-virus software will protect you.